SECURE LIVE MIGRATION OF TRUSTED EXECUTION ENVIRONMENT VIRTUAL MACHINES USING SMART CONTRACTS
US20240168787
2024-05-23
Physics
G06F9/45558
Inventors:
Assignee:
Applicant:
Drawings (4 of 10)
Smart overview of the Invention
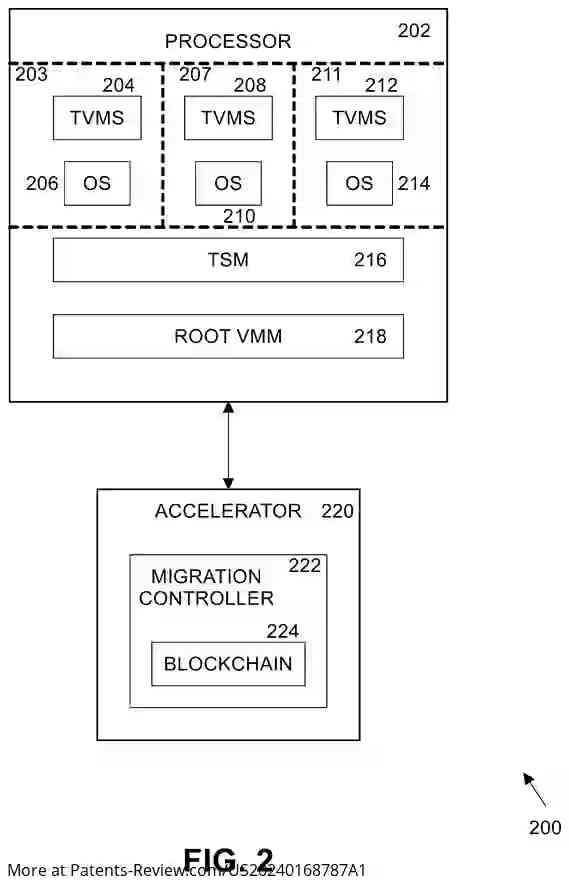
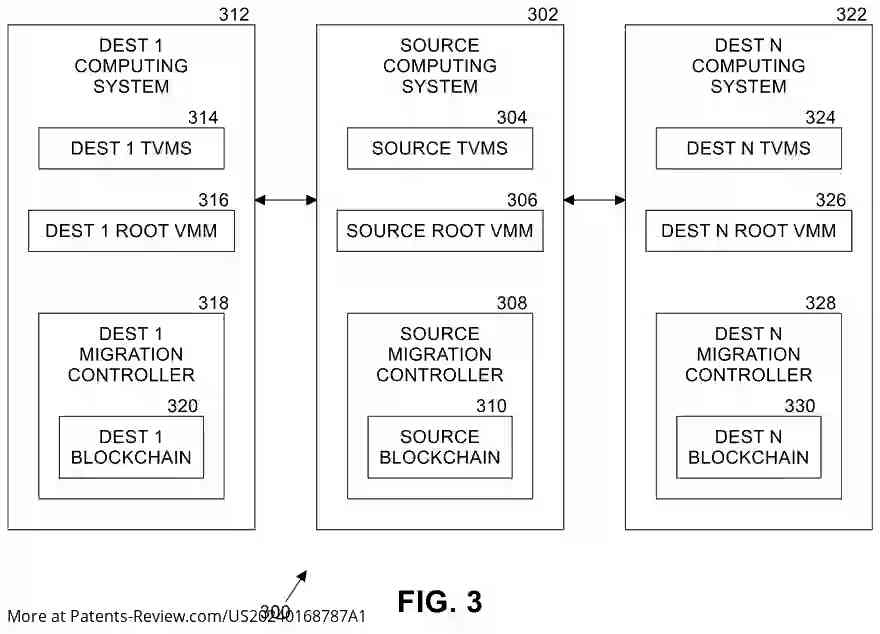
The technology presented focuses on enhancing secure live migration of Trusted Execution Environment Virtual Machines (TVMs) using smart contracts. It involves broadcasting a migration request to multiple destination systems, receiving bids from these systems, and allocating the TVM based on bidding prices. The migration process is automated and the allocation information is stored on a blockchain, ensuring security and transparency.
Field of Application
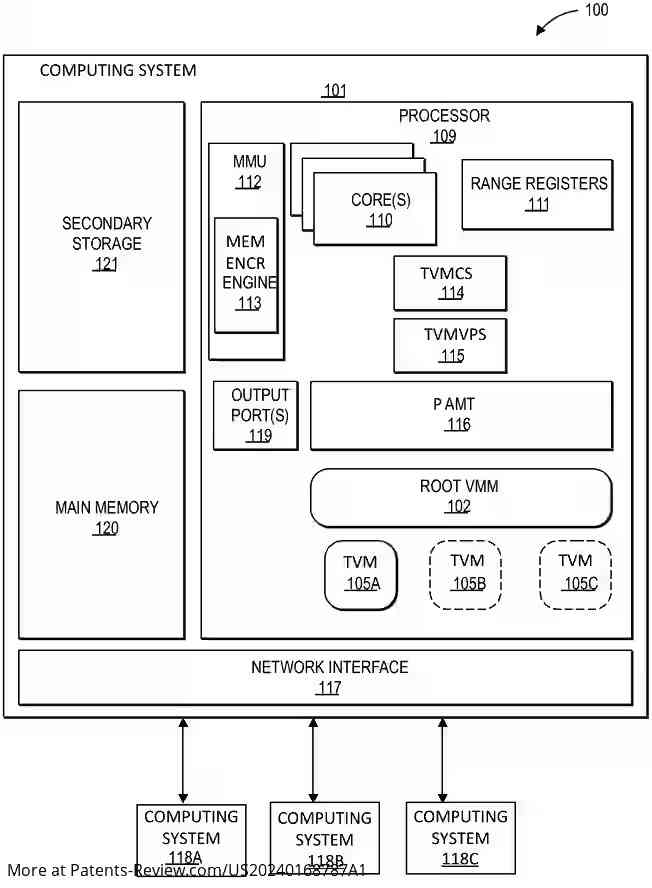
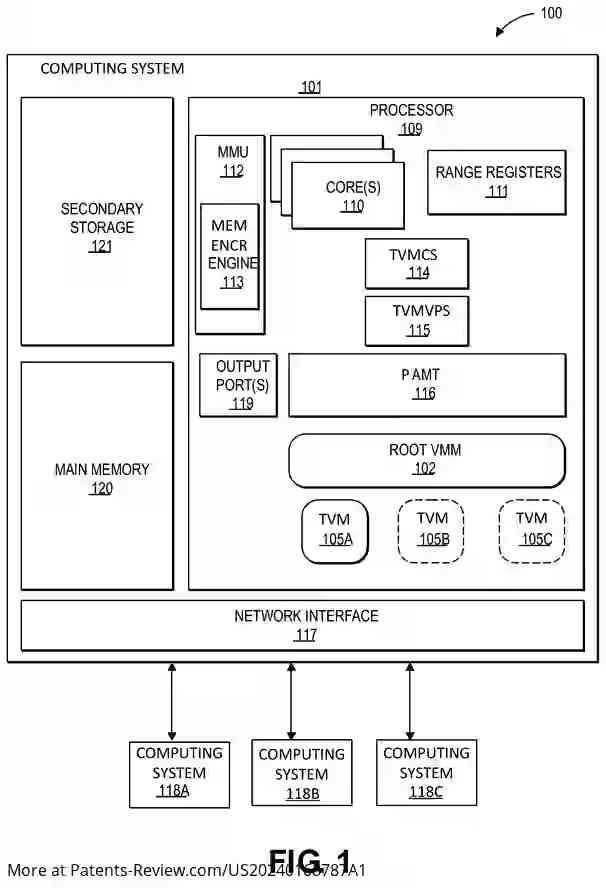
This technology pertains to the secure migration of processes within computing systems, particularly focusing on TVMs. These virtual machines operate within confidential computing architectures, such as Intel® Trust Domain Extensions (TDX), which isolate them from various software layers to protect against potential attacks. The solution addresses limitations in current migration methods, which are either disruptive (cold migration) or limited in scope (live migration).
Challenges in Current Systems
Existing live migration techniques require manual configuration changes by cloud service providers (CSPs), which can be cumbersome and inefficient. These methods are typically restricted to one-to-one migrations and involve significant manual intervention to align system configurations between source and destination environments. This manual process not only increases the workload but also introduces potential points of failure or security risks.
Proposed Solution
The disclosed method allows for the automatic live migration of TVMs across multiple destination systems without requiring manual adjustments by CSPs. It leverages blockchain technology to securely document migration allocations, enhancing both efficiency and security. While primarily discussed in the context of Intel® TDX, the method is adaptable to other confidential computing architectures like AMD® SEV or ARM® RME.
Technical Details
The solution integrates with various processor types and computing devices, ensuring broad applicability. It provides cryptographic isolation for workloads through technologies like Secure Memory Encryption (SME) and Secure Encrypted Virtualization (SEV). The approach facilitates maintaining confidentiality and integrity in cloud environments by removing CSP software from the trust boundary, thus offering a robust infrastructure for secure virtual machine operations.