DISTRIBUTED IDENTITY MANAGEMENT FOR A DECENTRALIZED PLATFORM
US20250015994
2025-01-09
Electricity
H04L9/32
Inventors:
Assignee:
Applicant:
Drawings (4 of 4)
Smart overview of the Invention
The patent describes a method for managing distributed identities (DID) on a decentralized platform. This method utilizes an engine executed by a processor to generate cryptographically secure and reusable identities for users, which obfuscate the actual identity of the owner. These identities are associated with a blockchain, ensuring security and privacy. The engine also controls access to digital information and services linked to these identities, enhancing user privacy and control.
Field of Invention
This innovation pertains to the management of distributed identities within decentralized platforms. It addresses the limitations of traditional centralized systems where a third-party authority can manipulate, censor, and control user data and identities. The decentralized approach aims to provide users with greater control over their digital information and ensure anonymity.
Background
Traditional digital systems rely on central server architectures managed by third-party authorities, posing security risks due to a single point of control. These systems require verifiable user identities for access and ownership validation, limiting user anonymity. Users demand more control over their digital information and secure, anonymous identity management. The current lack of decentralized mechanisms for sharing digital information highlights the need for this innovation.
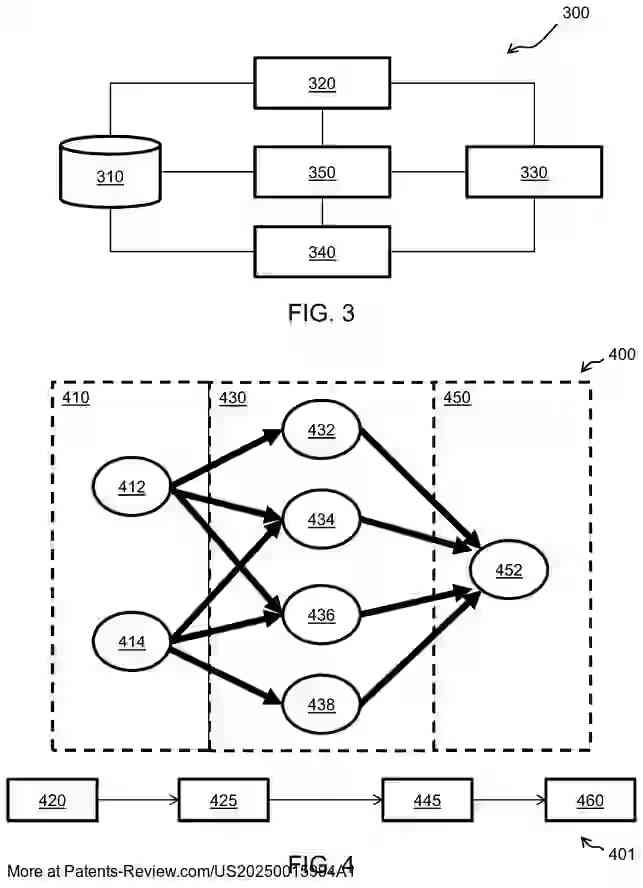
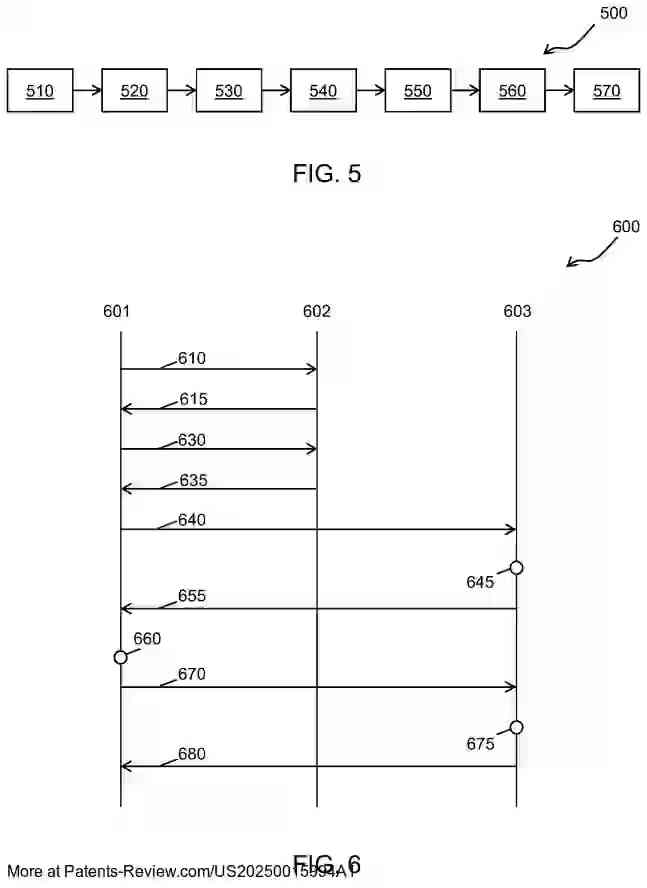
Summary and Implementation
The method involves generating secure distributed identities that are linked to a blockchain, eliminating the need for centralized authentication services. Access to digital information is gated through an owner authorization flow, contrasting with conventional approval processes. This method supports private social media activities without third-party interference, transforming the decentralized platform into a secure environment.
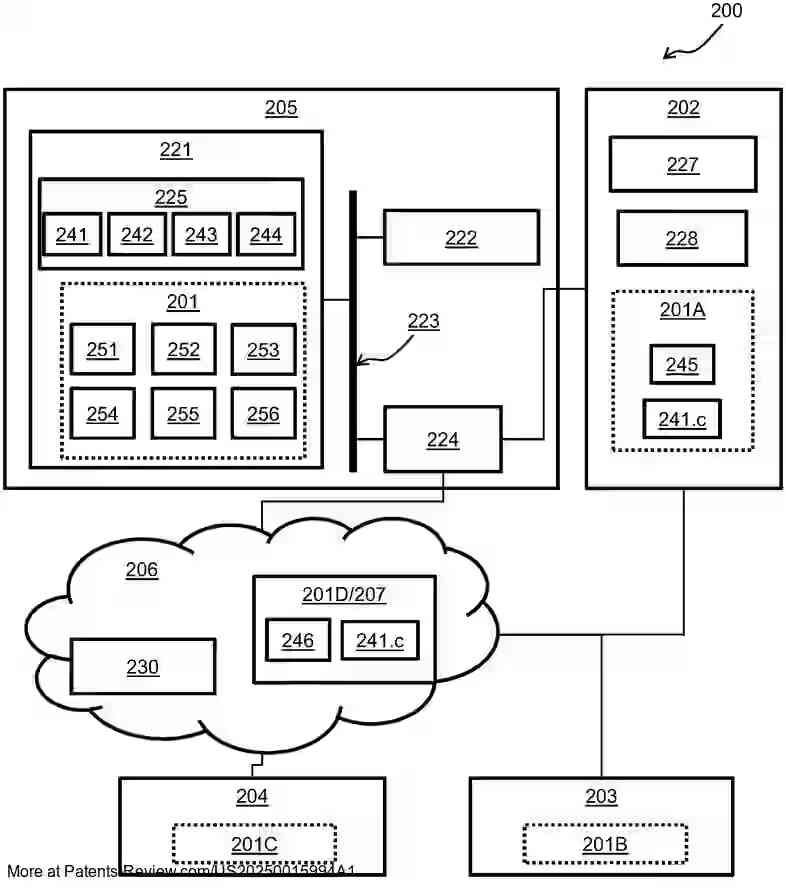
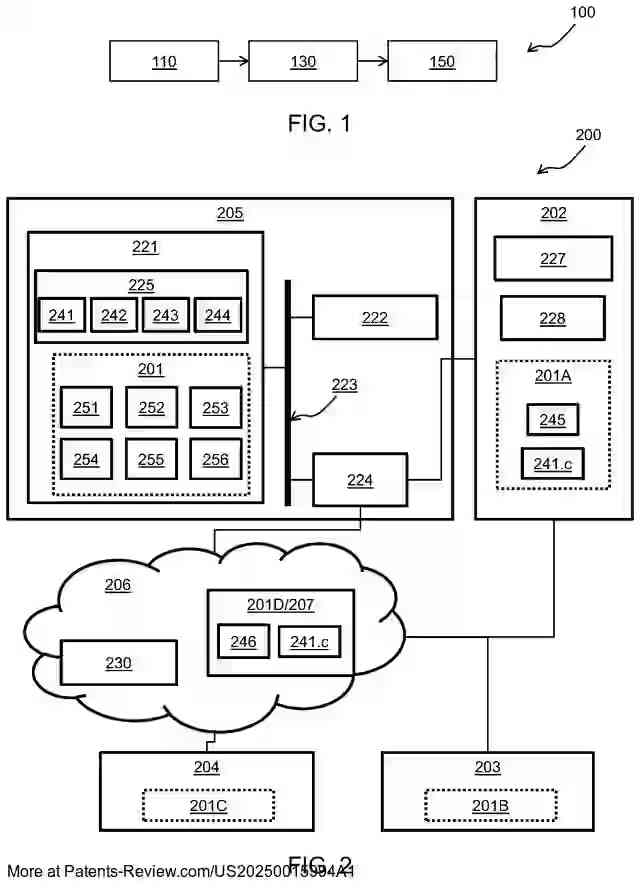
Architecture and Advantages
The architecture includes various nodes such as devices, computing platforms, servers, and networks, all contributing to a decentralized platform. The engine operates across these nodes using public and private key pairs to secure identities and regulate access. This setup allows for peer-to-peer connections without central server dependencies, enabling secure social networking experiences. The system is scalable and modular, supporting diverse devices and configurations.